Shell network operations
May 23, 2021 Shell - An example of programming
Table of contents
Objective
The previous sections have covered the operation of the shell programming paradigm values, Boolean values, strings, files, file systems, processes, and so on. These contents basically cover all aspects of the normal operation of a separate machine in the network, now need to extend the perspective from a single machine to these machines through a variety of network equipment and protocols connected to the network world, analysis of network topology, network working principles, understanding of a variety of common network protocols, a variety of common hardware working principles, network communication and security-related software and working principle analysis.
However, because network-related issues are so complex, it is not possible to describe specifics here, so if you want to know more details, it is recommended to refer to the relevant information. But Linux is a good platform for learning and practicing network principles, not only because its own implementation of the network architecture is open source, but also because there are countable analytical tools and libraries, so if you are a student, don't miss it to do the relevant practical work.
Introduction to the principles of the network
Our online world
Before you do all the introductions, get a visual look at the real online world. W
hen I write this
Web
the web editor, I listen to remote music with
mplayer
and when I'm tired, I turn on
TV
and start watching Phoenix TV...
These "modern" lives, I think, would have been unthinkable without the Internet.
Here's a beautiful picture of the online world:
While staring at the monitor, while tapping the keyboard, while hanging headphones.
The host power lamp is brilliant, with a green light, it is easy to imagine that the network card position behind the host must have two different colors of light flashing, it shows the host is in contact with the computer network world.
Just in a corner of the lab, there is a switch on a network port of the network cable connected to the host, the switch received a LAN gateway, and then the gateway received a router in the information building, and then transferred to the school network center on another router ...
During this time, one router is connected to the blog server, the other may be connected to
TVserver, and the other is connected to a music server at the head of the telecommunications network...
dia
"network map" with dia:
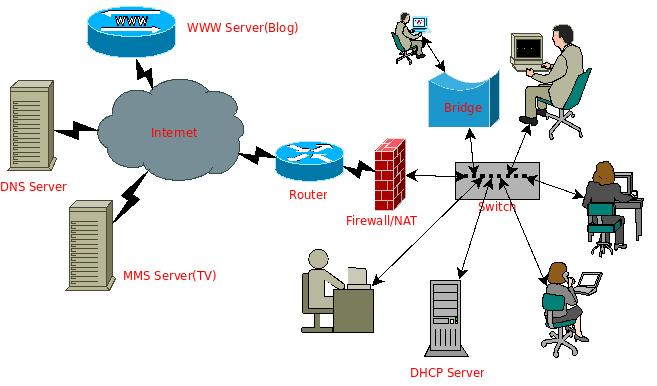
The diagram shows some of the most common network devices and network services, including local hosts, routing, switches, bridges, domain name servers, World Wide Web services, video services, firewall
IP
services and so on.
Various of these devices make up the entire physical network, while network services are the various network applications built on these devices.
Today's web applications are becoming richer and more diverse, such as instant chat
IM
p2p
resource sharing, web search, etc., how do they work, how do they build on a wide variety of network devices, and work safely and efficiently?
This depends on the development, implementation, and application of the gradually improved network architecture and various related network protocols.
Introduction to network architecture and network protocols
So what is the network architecture like? W hat are the relevant network protocols involved? What is a network protocol?
In the book "Computer Networks - Top-down Approach", the metaphor of network architecture layering is given very cleverly, and it is easy to understand the comparison between the various layers of the network and the various links in the transportation system. I n the transportation system, the transport is people and goods, in the computer network system, the transport is electronic data. C onsider that both transportation and computer networks can eventually be classified as point-to-point information transmission. Consider the information transfer process between the two points here to get such a contrasting relationship, as shown in the figure below:
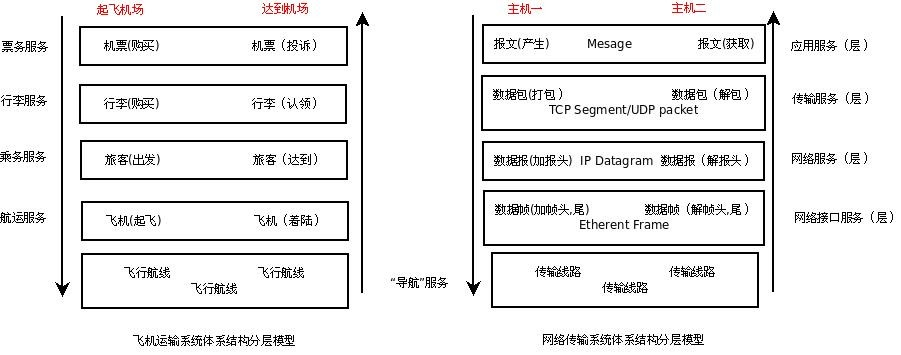
In contrast to the figure above, it is easier to understand the hierarchical principle of the right-hand network architecture (which may be easier to understand if the intermediate process is received by sending a letter), and on the right side of the figure above is a network hierarchical diagram
TCP/IP
network architecture, where a variety of "packaging" operations are required before data is sent to the network, and after receiving data from the network, a "unpacked" operation is required, resulting in the extraction of pure data information. T
his layered approach is for the need to transfer data and how to establish a connection between the two hosts and how to ensure the integrity and reliability of the data transfer. B
y spreading needs at different levels, the entire architecture becomes clearer and clearer.
These "requirements" are regulated by a variety of corresponding protocols, which become network protocols.
The
OSI
model (layer 7) compared to the
TCP/IP
model (layer 4) can be seen from the following image (from the network):
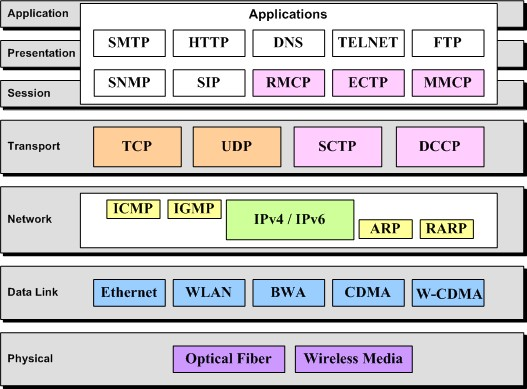
The following image (from the network) more clearly reflects
TCP/IP
hierarchical model.

The above describes the basic content of network principles, if you want to learn more about network principles and operating system support for the implementation of the network, you can consider reading the reference materials later. Here are some practices on how to network under Linux, how to build various network services with Linux, and network security considerations, as well as basic network programming and development.
Linux under the network "real battle"
How to connect our Linux host to the network
If you want a system to be connected to the Internet, the first thing is of course to build a physical network.
The physical way to access the network is quite a lot, such as directly using the network cable to connect to Ethernet, using wireless network card to access the Internet,
ADSL
dial-up Internet access ...
For the common way to use Ethernet network card to access the network, after building the physical network and ensuring that the
IP
and the default gateway, which can be obtained by manual configuration and dynamic acquisition of two ways.
Example: Get an IP address through dhclient
If the local area network you
DHCP
you can get it this way,
N
the device name, and if there is only one network card, it is usually 0 or 1.
$ dhclient ethNExample: Static configuration of IP addresses
Of course, you can also consider a static configuration in
ip_address
the IP address of the
IP
gw_ip_address
is the IP address of the gateway to
IP
$ ifconfig eth0 ip_address on
$ route add deafult gw gw_ip_address
If it doesn't work, remember to check the network card for drives with tools such as
ifconfig/mii-tool/ethtool
then check the type of network card (or through the manual that came with the motherboard manual and the separate network card) through tools such as
lspci/dmesg
insmod/modprobe
Build a bridge with Linux
The bridge works on
OSI
model, the data link layer, and it only needs to know the MAC address
MAC
the target host to work. T
he Linux
2.2
so let's take a look at
the next resources.
If you want to configure a Linux host as a bridge, you need at least two network cards.
The role of the bridge is equivalent to a network cable, the user need not care what is inside, connect its two network port to two hosts can let the two hosts support communication with each other.
However, it is more powerful than a network cable, if equipped with a firewall, you can isolate the network segments connected to both ends of it (note that
IP
not recognize IP), in addition, if the bridge has multiple network ports, then you can achieve a complex function switch, and if you effectively combine multiple bridges, it is possible to achieve a complex firewall system that can achieve traffic control and load balancing.
Route with Linux
Routing works
OSI
model, the network
router
which can configure routes for Linux, and of course, there are many tools under Linux that support dynamic routing.
Relevant information is spread through the Internet, due to time relations, here is not to introduce.
Build a variety of regular network services with Linux
What network services do you need?
-
Get a DHCP server
DHCPthen get adhcpdsee the references; -
If you want to get a mail server, install
sendmailorexim4 -
If you want to get another mailing list server, install
mailman -
If you want to get a server to receive mail, install a
pop3server; -
If you want to
website, get anapacheornginxserver; -
If you want to get a firewall service, configure
netfiltertooliptables
What's more? If you can imagine, linux basically has a corresponding implementation.
Network problem diagnosis and maintenance under Linux
If there is a network problem, don't panic, step by step check all levels of the network: physical links, link layers, network layers up to the application layer, familiar with the use of various tools such as
ethereal/tcpdump
hping
nmap
netstat
netpipe
netperf
vnstat
ntop
For detailed information on the use of these tools and on the diagnosis and maintenance of network problems, see the follow-up information.
Network programming and development under Linux
If you want to do network programming development, such as:
-
To implement a
/architecture, you can use socket programmingsocketLinux; -
If you want to write a packet capture and protocol analysis program, you can use
libpaplibraries; -
If you want to implement a protocol, you can refer to the relevant
RFCdocumentation and implementsocketprogramming.
This can refer to related
Linux socket
and other materials.
Postscript
Originally introduced some basic content related to the network, but due to time relations, did not elaborate, more details please refer to the relevant information.
At this point, the entire Shell Programming Paradigm is a rough one, but the Samples lack examples, especially in this section. Therefore, if time permits, some instances are gradually added.
Resources
- Computer networks - top-down analysis methods
- Linux Network Architecture (published by Tsinghua University Press)
- Linux System Troubleshooting And Troubleshooting Chapter 13 Network Problems (People's Post and Telecommunications Press)
- Dial-up Internet access under Linux with ADSL
- Wireless network-related data collection under Linux
- The implementation analysis and use of Linux bridge
- DHCP mini howto
- The best 75 security tools
- The knowledge that network administrators must have
- Two tools for detecting rootkits on Linux: Rootkit Hunter and Chkrootkit
- Simple analysis of packet capture and ip protocol (based on pcap library)
- Rfc
- An instance of the C-language programming implementation of the HTTP protocol